Unknown Wordpress Exploit Abused to Compromise Thousands of Websites
Hackers have begun hijacking thousands of websites running the WordPress content management system (CMS) and are leveraging the websites to infect visitors with malware and exploits, security researchers reported Thursday.
The massive WordPress infection campaign began 16 days ago, but within the past 48 hours the numbers has drastically spiked, from roughly 1,000 infections per day, to close to 6,000 by Thursday, Daniel Cid, CTO of security firm Sucuri wrote in a blog post. Attackers are infecting users with servers hosting the Nuclear exploit kit, a common piece of malware sold on the black market. The exploit kit can abuse a victims machine in any number of ways.
“If you think about it, the compromised websites are just means for the criminals to get access to as many endpoint desktops as they can,” Cid explained. “What’s the easiest way to reach out to endpoints? Websites, of course.”
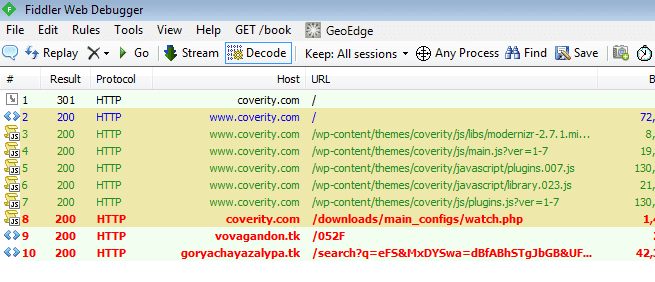
Thursday Sucuri security firm identified thousands of compromised websites, 95 percent of which were running on Wordpress. Security researchers were not yet able to identify exactly how the websites were compromised, but believe the vulnerability could stem from a vulnerability within a Wordpress plugin. Google took swift action, almost instantly blacklisting 17 percent of compromised websites. Cid added that attackers managed to compromise Coverity security provider, and are abusing their website as part of their malicious malware redirection scheme and can be seen in the image below.
Sucuri has dubbed the infectious Wordpress campaign “VisitorTracker,” due to the function names used within their malware-laden javascript file named visitorTracker_isMob(). Cid did not publicly comment on any compromised web domains. To ensure your site is not infected, Sucuri has a free web scanner to ensure your website is safe and secure!