Bash Shell Vulnerability Affects Linux, UNIX and Mac OS X
A critical vulnerability in the Bourne Again Shell, commonly referred to as Bash, which is currently present in most Linux and UNIX distributions as well as Apple’s Mac OS X has been discovered and administrators are begin urged to patch their systems immediately.
The (CVE-2014-6271) vulnerability affects versions 1.14 through 4.3 of GNU Bash and is begin called Bash Bug and ShellShock by security researchers online.
For some background information, Bash is present everywhere on Linux and UNIX systems, and the severity of Bash bug compares to the severity of the Heartbleed OpenSSL vulnerability. The Bash bug was discovered by Stephane Chazelas, a Linux and UNIX network and telecom administrator.
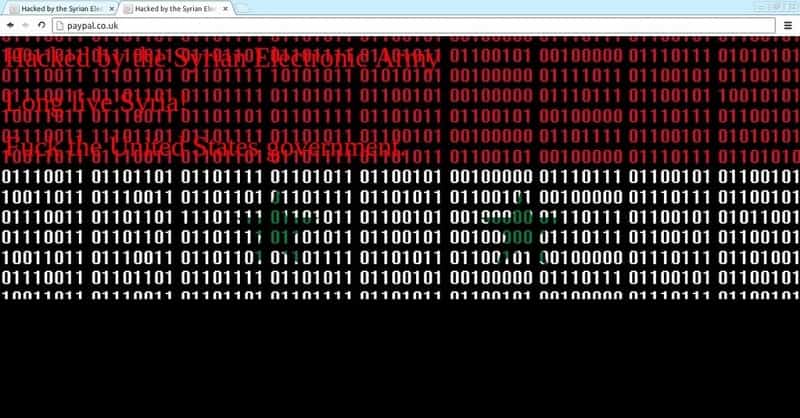
According to researchers an attacker could remotely attach a malicious executable to any number of documents that invoke the use of Bash when executed to abuse Shellshock. From there, attackers can execute shell commands remotely on a target machine using crafted variables. “In many common configurations, this vulnerability is exploitable over the network,” Stephane said.
The 22-year-old vulnerability stems from the way bash handles specially-formatted environment variables, namely exported shell functions. When assigning a function to a variable, trailing code in the function definition will be executed.
Patches regarding the Bash Bug or Shellshock are starting to be released from prominent Linux distributions including Red Hat, Debian, Ubuntu, CentOS and others. Distributors started issuing patches immediately after learning of Chazelas research.
The Bash Bug or Shellshock vulnerability has put millions of machines at risk. While bash is not directly used by remote users, it is a common shell for evaluating and executing commands from other programs. According the researchers, if an applications calls on the Bash shell command via web HTTP or a Common-Gateway Interface (CGI) in a way that allows a user to insert data, the web server is vulnerable and can be hacked.
Simply put, if Bash has been configured as the default system shell, attackers can launch malicious attacks and inject code on the server by sending specially crafted malicious web requests by setting headers in the web request, or by setting weird mime types. Proof-of-concept code for the cgi-bin reverse shell has been posted online.
Similar attacks are also possible via OpenSSH, “We have also verified that this vulnerability is exposed in ssh—but only to authenticated sessions. Web applications like cgi-scripts may be vulnerable based on a number of factors; including calling other applications through a shell, or evaluating sections of code through a shell,” Stephane warned. If an attacker does not happen to have an SSH account, this exploit would not work.
The severity of this bug is similar to Heartbleed as warned earlier, NIST vulnerability database rated Bash Bug or Shellshcok a “10 out of 10” in terms of severity.
To determine if your Unix or Linux system is vulnerable, you can run the following commands:
- env X=”() { :;} ; echo shellshock” /bin/sh -c “echo completed”
- env X=”() { :;} ; echo shellshock” `which bash` -c “echo completed”
If the word Shellshock appears during the output, your system is vulnerable.
If your system if vulnerable it it highly recommended you upgrade your bash package as soon as possible.