Following Lenovo, Dell Ships PC’s with Rogue Level CA Certificate
Following in the footsteps of this years Superfish that hit Lenovo in February, Dell is now shipping out computers that come pre-installed with a digital certificate that makes it easy for attackers to cryptographically impersonate Google, Amazon, Bank of America among other HTTPS-protected sites.
The self-signed transport layer security certificate, which was issued by an entity titled eDellRoot, was found pre-installed as a root certificate on at least two models of Dell Laptops, including an Inspiron 5000 series notebook and an XPS 15 model. However the list of affected models could extend, as reports that Dell Insiprion Desktops, Precision M4800 and Latitude models may be affected. Both certificates on the computers are signed with the same private cryptographic key. Meaning anyone with a more advanced technical skillset can extract the key and use it to sign fraudulent certificates for any HTTPS-protected website visited through the computer. Depending on the browser, all Dell computers shipped out with the rogue certificate will accept faulty encrypted web sessions with zero warnings to the end user whatsoever.
The discovery came over the weekend after a twitter user Joe Nord posted a screenshot of the certificate. Shortly following, Dell customers crowdsourced information, sharing technical details on their version of the eDellRoot certificate secretly installed on Dell machines. Joe Nord posted a screenshot as it appeared in the Microsoft Management Console.
Nord also included certificate details with the fingerprint of the private key that underpins it.
Following Nord’s series of tweets, another Dell customer took to Twitter, heavily scrutinizing the eDellRoot certificate for being signed with the same private keys. The individual went on to warn Dell officials that the inclusion of the certificate is a major security concern, due to installing the exact same CA on an unknown number of other machines.
Nord said that he visited this bogus HTTPS test site, which was developed by security expert Kenn White, using the private key found on the eDellRoot certificate. Nord said that Google Chrome, Internet Explorer and Microsoft edge browsers all established an encrypted web session with zero warnings, even though it was clearly not secure. Fortunately, FireFox alerted users proceeding to the site, warning their connection was not secure.
Dell addresses eDellRoot certificate
Following the fiasco, Dell officials apologized for shipping out systems with the eDellRoot certificate and promptly issued a software tool that removes the rogue certificate.
As many suspected, the eDellRoot certificate is associated with Dell’s product line, company officials wrote in a blog post published late Monday night. The certificates were installed for the purpose of making it easier for customers to maintain their machines. In attempt to de-associate Dell’s rogue certificate with Lenovo’s SuperFish man-in-the-middle adware that injected ads into HTTPS-protected web pages, Dell officials wrote:
“The certificate is not malware or adware. Rather, it was intended to provide the system service tag to Dell online support allowing us to quickly identify the computer model, making it easier and faster to service our customers. This certificate is not being used to collect personal customer information. It’s also important to note that the certificate will not reinstall itself once it is properly removed using the recommended Dell process.”
How to remove the eDellRoot Certificate
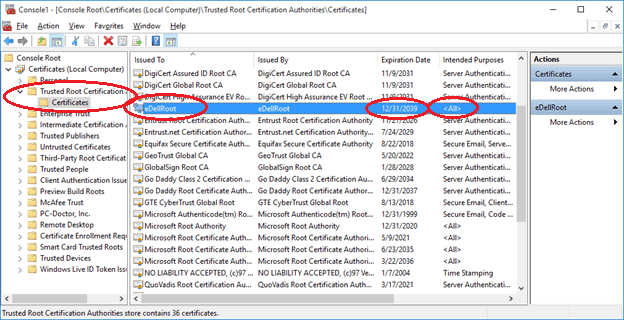
Customers affected by Dell who have the eDellRoot certificate installed can download the official uninstaller app from Dell. Dell has also provided manual instructions for the removal of the eDellRoot certificate. Dell customers can manually check for eDellRoot by completing the following:
- Go to the start menu, type “certmgr.msc” and hit enter
- Navigate into Trusted Root Certification Authorities
- Navigate into the the Certificate folder
- Check and see of eDellRoot is installed
If eDellRoot is installed on your system you should right click and delete the certificate immediately.
Dell’s response to the incident is a good start, but if Dell wants to regain serious customers they need to explain how such a critical failure went unnoticed or was allowed pre-installed on the system in the first place.
[Photo via Jjpwiki/Wikipedia (CC BY-SA 4.0)]