Android Ransomware, Simplocker, Encrypts Files Appearing to be FBI
A little over a month ago we saw the first Android ransomware, Simplocker, that encrypts SD card files, and just last week we saw the Android ransomware, ScarePakage, that holds the device hostage appearing to be the FBI, now Simplocker has emerged into a deadly ransomware housing features of both malwares.
Security researchers at ESET have identified a number of Android/Simplocker variants crawling the web and infecting Android based smartphones. Researchers have noted the variants feature significant developments.
Of the past two malwares merging and becoming one powerful ransom tool, the malware not only takes over the device stating it is the FBI demanding $300, it encrypts the devices files too. The ransom is significantly lower than the original Scarepakage $500 fee, but the fee skyrockets from Simplocker’s previous $21 demand. The ransom screen is an identical copy of recently uncovered ScarePakage malware, but contains the hardcoded functionality of both malwares. “This is not uncommon in the malware world, malware is often assembled from various parts and we sometimes even see code apparently from various sources, possibly Copy&Pasted, and so on,” Robert Lipovsky, ESET Malware Researcher told FreedomHacker in an email.
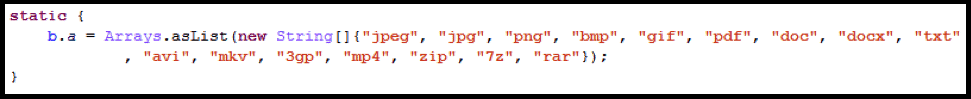
Previously, Simplocker encrypted all common file types from known photo extensions, to video extensions, to a number of audio and common document type extensions. Research states that the file-encryption technology is virtually untouched, apart from it using a different encryption key. Only two small changes were made to make victim’s lives much more difficult. While nearly all important information becomes encrypted, Simplocker developers have added functionality to encrypt archive files, which include: ZIP, 7z, and RAR. Many commonly used Android backup tools store in an archive format. Now Simplocker can encrypt the backups as well, making it much harder to restore the phone.
For the malware to take over the phone, it has to be given Device Administrator permissions. Cybercriminals are injecting the malware into popular applications such as Adobe Flash or commonly used anti-virus providers and asking device holders for administrator permissions to install the application. Once the ‘install’ is completed, the screen is instantly locked and turns into an FBI ransomware screen. In the past, police ransomware was being injected into faulty pornography pages and locking the screen going forward, but was easily removed. Simplocker is far more comprehensive than it’s past versions.


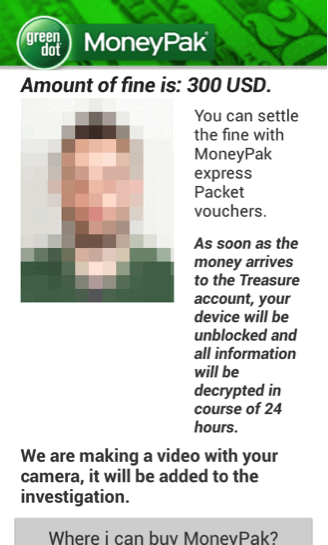
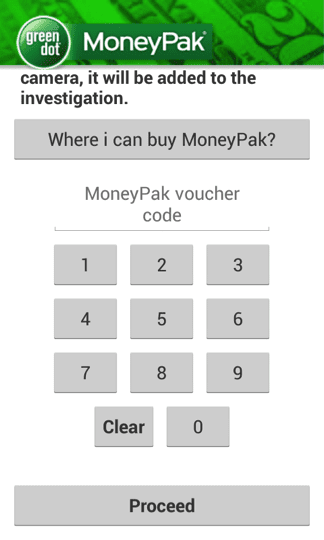
Image Credit: WeLiveSecurity
“The sites where one can come across these either malware-laden or simply malicious apps also differ,” Lipovsky told us in an email. “Yes, it can be on porn sites, warez sites, but also various alternative markets, forums and malware is occasionally found even on the official Google Play Store.”
The progression of the malware only one month later is staggering to say the least. Lipovsky told us Simplocker is being sold on underground forums for $5,000, which leads us to believe why variants progressions have significantly improved.
How To: Removal and Prevention of Android/Simplocker
As Simplocker is the first of its kind, there are a number of precautions that can be taken or prevent the malware alongside remove it if one falls victim to the social engineers.
Steps to Prevent Simplocker as recommended by Robert Lipovsky, ESET Malware Researcher
- Download apps only from trustworthy sources (e.g. Google Play) and from trustworthy developers
- Examine the permissions requested by an app during installation, don’t just do the old “next-next-yes…”. If there’s anything suspicious (e.g. an app requesting access to messages, contacts, GPS, whatever for no apparent reason), don’t install it.
- Use an updated antivirus on your device
Process to Decrypt Files Taken Hostage by Android/Simplocker
“Simplocker can be removed without paying the ransom, although the new version is more difficult to remove because of the Device Administrator. Users that have had their files encrypted can retrieve them using the ESET Simplocker Decryptor: http://download.eset.com/special/ESET-Simplocker-Decryptor.apk,” Lipovsky tells us.
Simplocker appears to be evolving at rapid rates as it is being sold on underground forums and the file encryption mechanisms continue to enhance.