Critical Zero-Day Vulnerability in WordPress Comments Could Expose Admin Password
The largest blogging platform in the world is under attack, yet again, with another zero-day vulnerability disclosed that affects every version of Worpress prior to their latest 4.2.1 update. The vulnerability is so severe your Wordpress website could be hacked with a simple comment.
WordPress, the most popular content management system on the web today was hit with a fresh zero-day vulnerability that allows hackers to expose the WordPress admin password with a simple comment. Finnish security company Klikki Oy, disclosed the WordPress XSS comment vulnerability Monday, releasing both video and proof of concept code demonstrating how the comment has the ability to expose the WordPress admin password.
The XSS flaw allows hackers to store malicious JavaScript code on Wordpress site via the comment section. Normally, the WordPress site would block these types of comments as it could be abused to send visitors username and password credentials to the hacker, which is known as a Cross-Site Scripting (XSS) Attack. For this attack to execute, all it takes is a visitor’s browser to read the code on the affected webpage.
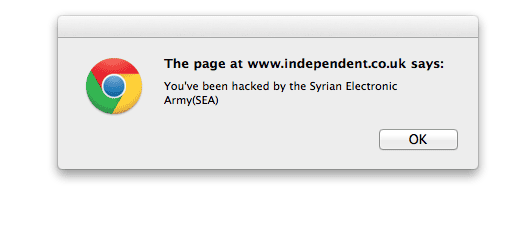
If the website owner (logged-in) visited the affected page, the attacker can leverage the vulnerability and continue to execute arbitrary code, leading to the hacker stealing your credentials and hacking your site. “Alternatively the attacker could change the administrator’s password, create new administrator accounts, or do whatever else the currently logged-in administrator can do on the target system,” Jouko Pynnönen of Klikki Oy warned in their blog post disclosing the WordPress XSS vulnerability.
Pynnönen’s video demonstrating the XSS comment flaw in real time can be seen below:
Another security researcher, Ryan Dewhurst, founder of the WordPress vulnerability database WPScan, said the attack worked during his testing and posted his own proof-of-concept code on Github. He noted the attack requires the hacker to already have a previously comment, so the exploit code could easily bypass the built-in WordPress comment filter. Many blogs today don’t require users to have previously approved comments, meaning WordPress sites could easily be hacked with one simple comment.
To leverage the zero-day and inject malicious JavaScript into the comment system, the hacker must first make their comment long enough so that the data received by the MySQL database is equal to 64KB. This will trigger an error, allowing the malicious code to bypass the comment filter and execute.
Within hours of the zero-day WordPress comment flaw being exposed, the WordPress team issued an immediate security patch, updating the entire WordPress core to 4.2.1. All versions previous to the latest 4.2.1 patch are vulnerable to the WordPress XSS comment flaw. To help fend off similar attacks that may occur in the future, you can use Akismet to help block spam and malicious queries from making their way into your comment que.
Just last week, WordPress released 4.1.2, patching eight critical vulnerabilities, one of which exposed a similar cross-site scripting flaw that could allow hackers to easily hijack your WordPress website. The same-day, another security firm disclosed that dozens of WordPress plugins were plagued with another XSS flaw, unrelated to WordPress 4.1.2.
Roughly twenty percent of the entire web today runs on Wordpress, with recent disclosures, that scale could be worrisome to the millions of vulnerable WordPress sites still online.
If you run or manage a WordPress site, upgrade to WordPress 4.2.1 immediately by going to Dashboard > Updates. To prevent against future attacks, install a comment spam plugin and require visitors comments to be manually approved.