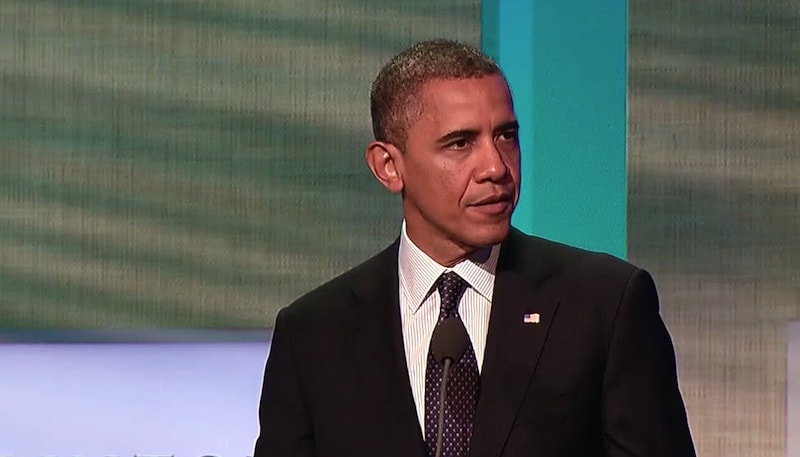
Russian Hackers Breach Obama’s Unclassified Email Network
The same Russian hackers who gained access to the White House network last year were able to breach and read President Obama’s unclassified emails, accessing possibly sensitive information.
The White House breach was far more severe than initially admitted when the systems had first been hacked last year. The discovery of the cyberattack led to a temporary shutdown of the White House email system to mitigate the threat.
The Russian hackers who breached President Obama’s unclassified email system did not appear to have penetrated any closely guarded servers or classified information from the White House network.
During their breach, hackers had access to a swath of email archives for people in the White House, and even some outside, with who President Obama communicated with, the New York Times reported. Hackers were able to access emails the president had sent and received, officials close to the investigation reported.
White House officials have assured that no classified information within their networks had been accessed or compromised during last years State Department breach. Many senior officials within the department have two computers, one strictly for operating on a highly secure classified network, while the latter is connected to the usual State Department network for unclassified communications.
Though the information was labeled as Unclassified, officials have concluded that the information accessed is still considered highly sensitive. Potentially sensitive information stored on the network include Obama’s schedules, email conversations with diplomats and ambassadors, discussion on pending legislation and debate on policy.
White House officials did not disclose how many of President Obama’s emails were accessed by hackers, nor the sensitivity of the emails contents. Obama’s email account wasn’t targeted or hacked itself, but the network used to transmit and store the unclassified emails and information was.
Senior White House officials and department security team’s have known of the scale of the attack for months now, but withheld information, downplaying the severity for several months.
“This has been one of the most sophisticated actors we’ve seen,” a senior official said speaking on the investigation.
Speculation has since been confirmed that the White House breach was so severe that officials met on a near daily basis for several weeks following the attack. Officials were particularly worried as the attack came from Russia, and presumably their government.
Behind department walls, the breach has spawned a new debate, questioning whether or not it is possible to protect the president’s digital presence, especially if it reaches past the highly secured networks of the executive branch.
Obama was issued a specially secured smartphone and list of close contacts he is allowed to exchange email conversations with from the device.
Earlier this month, White House officials reported the severe hacking had not damaged the departments systems, and that while elements may have been shut down to eradicate the threat, everything has since been restored.
The secrecy of the hack appears to be a major part in the governments downplay, where officials briefed on the attack chose not to disclose what the department knew was breached to possibly tip off Russians officials on what Americans learned from their internal investigations.
So where does the White House store classified information? The White House, State Department, Pentagon and intelligence agencies secure their most classified material on systems called Joint Worldwide Intelligence Commutations Systems, or Jwicks. This is also where top-secret and “secret compartmentalized information” is stored within the government for officials cleared to view it. Senior officials say there is no evidence these systems were pinpointed during the attack.