Android TowelRoot Vulnerability Allows Attackers Root Access
A recently uncovered vulnerability found inside the Linux kernel, was too found inside the Android operating system and could give attackers the ability to gain root access on vulnerable devices.
Researchers at Lacoon Mobile Security are dubbing the bug, “TowelRoot”, because it is the same vulnerability exploited in George Hotz (Geohot)’s latest Android rooting tool. If an attacker successfully exploited the Linux bug found within the Android operating system, it would give the attacker administrative access to the victim’s phone. With such access, an attacker could execute further malicious code, extract and upload data, bypass enterprise security applications including Samsung’s ‘secure’ Knox operating system, along with establish backdoors to abuse at a later date.
Security researcher at Bluebox security, Jeff Forristal, told Threatpost that the Linux futex vulnerability affects Android devices that run on the Linux kernel, and once the vulnerability was disclosed publicly, it was only a waiting game before someone developed an Android-specific exploit for it. George Hotz, a well-respected hacker in the jailbreaking and rooting scene, was the first one to take that step.
“This is pretty common practice/recipe in the Android rooting scene: they wait for a general-purpose Linux kernel vulnerability to surface, then they race to create an Android-specific exploit for it that can root the device,” Forristal told Threatpost.
The vulnerability is said to exist in Android versions 4.4 and earlier, and it said to be present on nearly every build, even including the new Samsung Galaxy S5. Other devices range from the Samsung Note 3, to LG phones, to Motorola, Razr, Sony Xperia, among hundreds of others.
“The vulnerability is currently codenamed TowelRoot after a rooting tool that was released on mobile forums that uses the vulnerability to root most of the popular mobile devices on the market. This tool is being widely publicized and is easily available for use without the need for technical know-how,” the blog post reports.
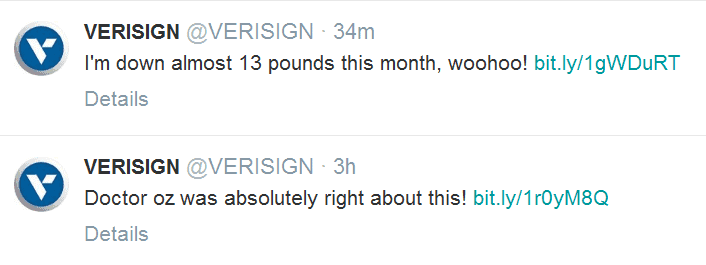
Currently the vulnerability is only accessibly via the rooting tool and has yet to appear in any malicious scams. Researchers note it is only a matter of time before the exploits begin to be distributed through various channels.
For an attacker to gain root access to a victim’s device, the attacker would need to craft an exploit package and pack it into a malicious application or executable. Researchers state users who avoid third party markets will be “immune” to the attacks, such seems untrue as many malicious applications have filtered into the Google Play store.
The risk of the Linux kernel vulnerability that is found inside the Android operating system is that unprivileged Android applications with malicious intent can exploit the kernel vulnerability for other malicious activities, not just root access intent.