TrueCrypt Warns Not Secure, Development Suddenly Shutdown
Is the largest open source hard drive encryption tool dead?
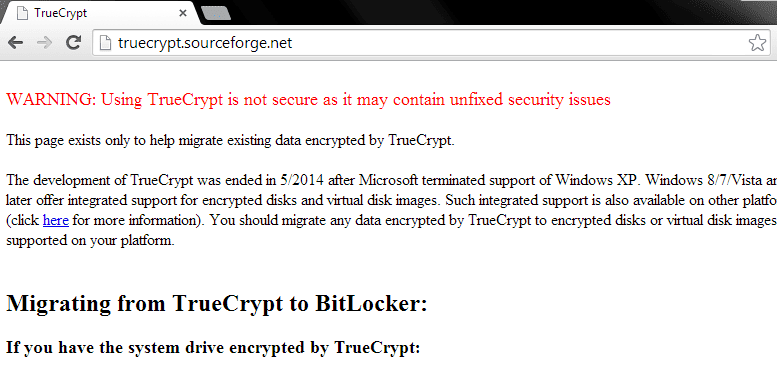
On May 28th, TrueCrypt, the popular encryption tool downloaded over 28 million times appeared to have closed its doors. The official TrueCrypt.org website appears to redirect to a SourceForge hosted page where users are greeted with a big red warning sign. The text warns that the open source encryption tool is no longer secure and notes that development for the project has been terminated.
WARNING: Using TrueCrypt is not secure as it may contain unfixed security issues
The development of TrueCrypt was ended in 5/2014 after Microsoft terminated support of Windows XP. Windows 8/7/Vista and later offer integrated support for encrypted disks and virtual disk images. Such integrated support is also available on other platforms (click here for more information). You should migrate any data encrypted by TrueCrypt to encrypted disks or virtual disk images supported on your platform.
The page also demonstrates how to migrate from TrueCrypt to BitLocker, Microsoft’s disk encryption software.
It is unclear whether the site has been hacked, defaced, or if the developers found a critical vulnerability or backdoor that could jeopardize the security of the software and its millions of users.
An audit of TrueCrypt was crowdfunded late last year to determine if the software was secure or if it was a honeypot, this came in light of Edward Snowden leaking documents about the depths of NSA spying. The results of the first TrueCrypt audit phase were released on April 14th by iSEC partners on behalf of the Open Crypto Audit Project, and no backdoors were found. The first audit of TrueCrypt was a success, and minimal issues were discovered. The first audit phase covered the TrueCrypt bootloader and Windows kernel driver.
A second audit phase is in the midst and has not yet begun, but will focus on whether encryption cipher suites, random number generators and critical key algorithms have been properly implemented.
Many experts are doubting the theory that the website has been hacked. A privacy and security researcher working on the TrueCrypt audit, Runa A. Sandvik, told Threatpost that the “current version listed on the SourceForge page, version 7.2, was signed yesterday with the same key used by the TrueCrypt Foundation for as long as two years.” Kaspersky lab researcher Costin Raiu, too confirmed this.
“With a defacement, you would usually just expect to see the website change. In this change, the software seems to have changed as well,” Sandvik told Threatpost. “The software has been modified to display a warning when you start it, as well as display a warning as part of the standard UI.”
Sandvik also noted she performed a small analysis on the newest TrueCrypt installer 7.2a, and saw no network traffic emerging from it.
“If the installer had a keylogger, you would expect the installer to at some point connect to another host and transfer information. Since there is no network traffic, there is no part of the installer that attempts to call home,” Sandvik stated. “Note that I just did a very quick analysis, a deeper dive might uncover sketchy bits and pieces.”
As noted above, the TrueCrypt version 7.2 was certified with the official TrueCrypt private signing key, suggesting the TrueCrypt shutdown wasn’t a hoax. Speculation has been going wild among Twitter and Reddit about the sudden shutdown. Whether or not it is a hoax, freedomhacker will continue to cover the story as it unfolds.